This guide is all about the SOCKS5 proxy and why it’s important today. A SOCKS5 proxy helps hide your IP address by sending your internet traffic through a server. It supports many types of traffic and even secure connections, making it great for those who need speed and security.
We’ll dive into what a SOCKS5 proxy does and how it’s different from older methods. You’ll learn about its secure socket capabilities and how they boost privacy and speed. We’ll also talk about setting it up, keeping your data safe, and how it can improve your online experience.
This guide is for IT experts, people who care about privacy, gamers, and torrent users in the United States. It’s easy to follow, with clear sections for setup, security, and performance tips. You can find what you need quickly.
Meta title: “The Ultimate Guide to SOCKS5 Proxies: Benefits and Uses”. Meta description: Learn how SOCKS5 proxy solutions deliver improved security, versatile secure socket support, and faster proxy performance for privacy, torrenting, and gaming.
Key Takeaways
- SOCKS5 proxy forwards TCP and UDP traffic through an intermediary server for IP masking.
- The socks5 protocol supports authentication and secure socket-style connections for added flexibility.
- Users gain faster proxy performance for applications like gaming and torrenting.
- We cover setup, security steps (including DNS leak protection), and performance tips.
- The guide targets IT pros, privacy-conscious consumers, gamers, and torrent users in the United States.
What is a SOCKS5 Proxy?
We start with the basics to help you understand the importance of a SOCKS5 proxy. It’s not just for web browsing. We’ll cover how these servers work, compare different protocols, and explain how traffic flows through a proxy.
Understanding Proxy Servers
Proxies are servers that act as middlemen between clients and websites. They can cache content, filter it, and keep users anonymous. There are two main types: forward proxies and reverse proxies.
HTTP and HTTPS proxies work at the application layer, handling web traffic. SOCKS proxies, on the other hand, operate at a lower layer and can handle various types of traffic. The SOCKS5 protocol is the latest version, offering more features than its predecessors.
Differences Between SOCKS4 and SOCKS5
We’ll look at the differences between SOCKS4 and SOCKS5. SOCKS4 only supports TCP and lacks authentication and IPv6 support. This makes it less useful for today’s applications.
SOCKS5, however, supports UDP, has multiple authentication methods, and works with IPv6. Its ability to handle UDP makes it great for services that need fast, reliable connections.
SOCKS5 also offers better protocol negotiation and authentication options. This makes it more flexible and suitable for a wide range of uses.
How SOCKS5 Works
We’ll break down how SOCKS5 works in simple steps. First, the client sets up a SOCKS5 endpoint and port in the settings.
Then, the client connects to the SOCKS5 server and performs a handshake. If needed, it exchanges authentication credentials.
The client sends a request, which can be for TCP, UDP, or inbound connections. The server then forwards the request to the target host and sends the response back.
We note that TCP and UDP are treated differently. TCP is proxied as streams, while UDP uses associations for datagrams. This allows non-HTTP protocols to pass through the proxy.
Finally, we mention that SOCKS5 doesn’t encrypt data by default. To secure data, it’s often paired with TLS, VPNs, or other secure protocols.
Benefits of Using SOCKS5 Proxies
We’ll explore how a SOCKS5 proxy improves our online activities. It enhances privacy, speeds up browsing, and offers flexibility. This makes it easier to choose where to use the socks5 protocol for the best results.
Enhanced privacy and anonymity
By routing traffic through a remote server, our IP is hidden. This means our device and location are less exposed when we’re online. It’s great for browsing, torrenting, or gaming.
However, data might not always be encrypted. Adding TLS or end-to-end encryption is key for secure tasks.
Improved performance
Using SOCKS5 can make browsing faster. It has fewer layers than many VPNs, which reduces latency. This is especially true for TCP and UDP traffic.
Proxies spread across different locations and use load balancing. This cuts down on the number of hops, boosting speed for local services.
Versatility for different applications
We can set up apps to use a SOCKS5 proxy individually. This gives us control over which apps use the proxy. It’s handy for specific tasks without affecting everything.
Support for TCP and UDP makes it versatile. It works well for web browsing, email, VoIP, BitTorrent, and gaming. This makes it useful across many platforms.
| Benefit | What it Means | Typical Use Cases |
|---|---|---|
| Enhanced privacy | Masks client IP by presenting the proxy endpoint | Anonymous browsing, torrenting, avoiding direct exposure |
| Improved speed | Less protocol overhead for TCP/UDP, regional endpoints | Faster proxy access to region-locked services, gaming |
| Protocol flexibility | Supports TCP and UDP for broader compatibility | VoIP, BitTorrent, browser-specific routing |
| Application-level control | Configure individual apps instead of the whole OS | Selective proxying for privacy and performance testing |
Common Uses for SOCKS5 Proxies
We explore how teams and individuals use SOCKS5 proxies. They are used for entertainment, file sharing, and competitive play. Each use has its own steps, limits, and tips for a stable connection and IP protection.
Bypassing Geo-Restrictions
We use a SOCKS5 proxy to make it seem like we’re in another country. This helps us access news sites, regional services, and streaming catalogs that are blocked in our area.
Some platforms check our account details and device fingerprints. They might block us even if our IP changes. Streaming services can also detect proxy pools and limit our access. It’s best to choose providers with many servers and fresh IP ranges for better results.
Torrenting Safely
Many torrent users choose a torrenting proxy for its support of tcp udp packets. This reduces overhead compared to a full VPN. Clients like qBittorrent, uTorrent, and Transmission let us set up SOCKS5 for each client, isolating P2P traffic.
SOCKS5 doesn’t encrypt by default. To avoid leaks, we should enable proxy authentication in the torrent client. Pairing the proxy with a VPN or client encryption settings helps keep our true IP hidden while maintaining high speeds.
Gaming Enhancements
A gaming proxy can reduce latency and hide our direct IP to protect against DDoS threats. It makes it easier to access region-locked servers by connecting through a server in the target region.
Many games use UDP for fast updates. It’s important to have SOCKS5 setups that support tcp udp forwarding. This ensures in-game packets pass without interruption. We test server locations and protocols before choosing a provider to ensure stable, low-latency sessions.
How to Choose the Right SOCKS5 Proxy
Choosing a reliable SOCKS5 proxy is about finding the right mix of speed, security, and openness. We’ll look at what matters, compare free and paid options, and highlight top providers. This way, you can find a solution that meets your privacy and performance needs.
Key Features to Look For
Look for providers that support both TCP and UDP. Many apps and games use UDP for better performance. Also, check if they offer username/password authentication to control access and prevent abuse.
Make sure they have clear logging and privacy policies. Providers that share retention limits and third-party audit results are more trustworthy. Having servers in different locations helps with accessing geo-restricted content.
Check the number of connections allowed, speed and bandwidth limits, and DNS leak protection. Also, confirm that the proxy works with common tools and platforms to avoid setup issues.
Comparing Free vs. Paid Proxies
Free SOCKS5 proxies are okay for occasional use. They often have bandwidth limits, unpredictable speeds, and may log your data or inject ads. Some free services sell your data to make money.
Paid proxies usually offer faster speeds and better privacy without ads. They provide clearer support, service expectations, and features like DNS leak protection and dedicated IPs.
For torrenting or gaming, paid services are better for stable speeds and legal safety. Paid plans help maintain performance under heavy use and offer quick support when needed.
Trusted Providers in the Market
Look at well-known brands that clearly document SOCKS5 support and setup. NordLayer and NordVPN offer SOCKS5 proxies with easy-to-follow guides. Private Internet Access (PIA) is a favorite among power users for its SOCKS5 proxy service.
Windscribe provides proxy features with strong privacy tools and helpful guides for gaming and Tor. Check their documentation for performance benchmarks and US-based support if you need local help.
When comparing providers, check independent tests, uptime records, and how they handle secure sockets and socks5 protocols. These signs help find truly trusted providers.
Setting Up a SOCKS5 Proxy
We’ll show you how to set up a SOCKS5 proxy. We’ll also cover common mistakes and how to fix them. Follow this guide for a secure and reliable connection.

Step-by-Step Configuration Guide
First, get the SOCKS5 server details from your provider. Make sure you have the address, port, and login info ready.
Open the app you want to use with the proxy. Set up proxy settings in your browser, torrent client, or gaming platform. Use extensions or built-in menus if you can.
To route all your traffic, adjust your OS proxy settings. This works on Windows or macOS. Or, use a tool like Proxifier to force apps to use the proxy. Choose TCP for most traffic, but enable UDP if your app and provider support it.
Check if everything works with tools like curl or netcat. A simple curl command can test the socks5 protocol and confirm routing.
Common Mistakes to Avoid
Typing wrong login details is a common mistake. Double-check your username, password, address, and port before testing.
Don’t forget to turn on the proxy in your app after setting it up. Many people forget this step.
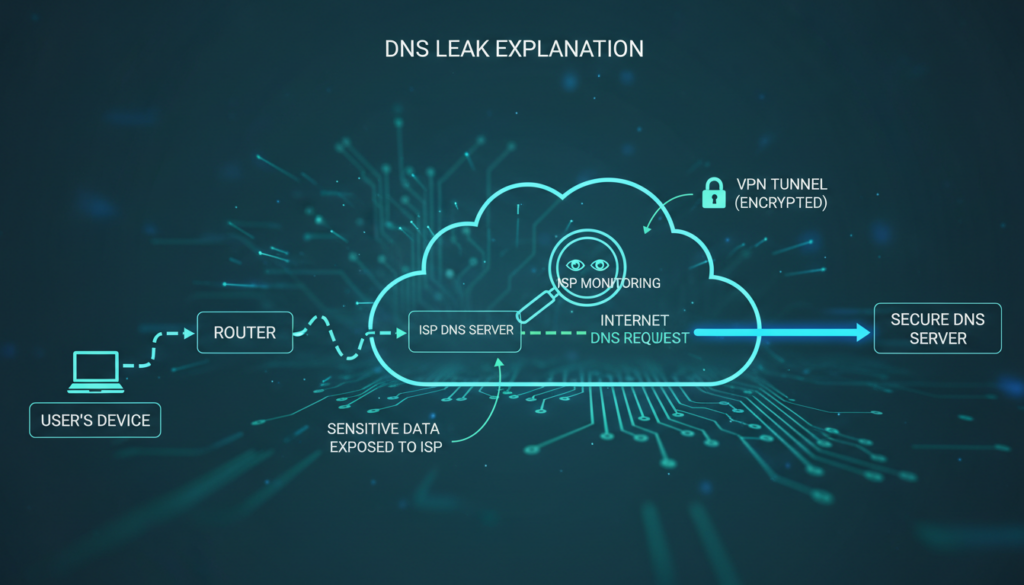
Remember, SOCKS5 doesn’t encrypt your traffic. It just routes it. Make sure your DNS is set up right to avoid leaks.
Be careful when using both a VPN and a proxy. Using one over the other can mess up your connection. Always keep authentication on unless you really trust the network.
Troubleshooting Connection Issues
First, check your server details and login info. If problems continue, check the provider’s status page for any issues.
Make sure your firewall or antivirus isn’t blocking the connection. Try allowing the client or test from another device to find the problem.
Look at logs for any errors during the SOCKS5 handshake. Logs can show authentication or protocol problems.
For deeper issues, use tools like Wireshark for packet capture. If it looks like a server problem, reach out to your provider’s support team.
Security Features of SOCKS5 Proxies
We look into how SOCKS5 proxies protect our online traffic. We’ll cover common ways to log in, encrypt data, and avoid DNS leaks. This helps keep our browsing and app use safe.
Authentication methods
SOCKS5 offers several ways to log in. You can choose no authentication for easy access but it’s not secure. A better option is username/password, which is safer and logs your sessions.
Encryption capabilities
SOCKS5 doesn’t encrypt data itself. It just routes TCP UDP streams. To keep data safe, we use TLS/SSL or SSH tunnels. These methods add security but might slow down your internet.
Protection against DNS leaks
DNS leaks can reveal where you’ve been online. Some clients send DNS queries through the proxy. If not, we use secure DNS methods or choose providers that block leaks.
| Area | Common Options | Recommended Practice |
|---|---|---|
| Authentication | None; Username/Password (RFC 1929); GSS-API (Kerberos) | Username/password or provider-managed keys with logging |
| Encryption | None native; TLS/SSL at app layer; SSH tunnels; VPN | Use SSH or VPN when confidentiality is required; TLS for app-level security |
| DNS Handling | Client-side proxy DNS; OS resolver; DoH/DoT; Provider DNS | Enable proxy DNS or DoH/DoT and verify dns leak protection |
| Protocols | TCP, UDP routing via SOCKS5 | Confirm tcp udp flows are proxied; test with provider tools |
SOCKS5 vs. Other Proxy Types
We compare common connection tools so readers can pick the right option for their needs. The differences affect speed, protocol support, and privacy.
Comparing with HTTP Proxies
HTTP proxies work at the application layer, focusing on web traffic. They handle HTTP and HTTPS, can rewrite headers, and offer caching for faster page loads.
On the other hand, the socks5 protocol is protocol-agnostic. A SOCKS5 proxy can carry various packets, including UDP traffic. This makes it more flexible for non-web communication.
SOCKS5 vs. VPNs
A VPN creates a network-level tunnel that encrypts all device traffic. SOCKS5 runs at the session or application level and usually does not add encryption.
SOCKS5 avoids tunneling overhead, making it faster for latency-sensitive tasks. A vpn protects everything on the device but may slow connections under heavy encryption. We sometimes use both for encryption and targeted routing.
Use Cases for Each Proxy Type
HTTP proxies are great for web-scraping, caching, and tasks focused on HTTP/HTTPS. They are efficient for repeated web requests.
We choose SOCKS5 for torrenting, gaming, and any app needing UDP or protocol flexibility. It’s a faster proxy for these tasks.
VPNs are best for full-device privacy, protecting sessions on public Wi‑Fi, and bypassing strict geo-blocks. They offer system-wide security that a single application proxy cannot match.
Performance Considerations
We look at how a SOCKS5 proxy impacts real-world speed and response time. Making small changes on both sides can make streaming, gaming, and big transfers faster.
Bandwidth and Speed Optimization
High-capacity backbones and servers close to you cut down on transit time. Plans without strict bandwidth caps help avoid slowdowns during busy times.
Lightweight encryption on the client side reduces CPU use and boosts speed. Choosing TCP for reliable transfers and UDP for real-time streams is key.
We suggest testing speed and setting up concurrent connections to match server limits. Traffic shaping policies at the provider level should favor low-latency flows for better bandwidth optimization.
Latency Issues and Solutions
Latency comes from extra routing hops, overloaded nodes, long distances, and inefficient ISP routing. Each adds milliseconds, affecting gaming and voice calls.
Choosing nearby servers and using providers with load-balancing helps. Enabling UDP when possible reduces delay for interactive apps.
Quality-of-service tools let us prioritize gaming or VoIP traffic. Regularly switching endpoints can reveal lower-latency routes.
Real-World Performance Tests
We run targeted tests to compare providers and locations. Speedtests to the proxy endpoint show raw throughput. Traceroute exposes routing hops and potential bottlenecks.
We measure ping and packet loss for gaming scenarios, then benchmark file transfers over TCP and UDP. Documenting results under different servers helps us choose the fastest proxy setup.
| Test | What We Measure | Why It Matters | Tip |
|---|---|---|---|
| Speedtest to Endpoint | Upload/download Mbps | Shows available bandwidth for transfers | Test at different times of day |
| Traceroute | Number of hops, routing path | Reveals inefficient ISP routes and extra hops | Compare routes between nearby servers |
| Ping & Packet Loss | Latency in ms, loss % | Key for gaming and real-time apps | Run sustained tests for accuracy |
| TCP File Transfer | Sustained throughput, errors | Shows reliability under congestion | Adjust concurrent connections |
| UDP Stream Test | Jitter, packet ordering, throughput | Reflects performance for voice/video | Enable UDP on provider when possible |
Integrating SOCKS5 Proxies with Applications
We show you how to add a SOCKS5 proxy to common apps. This ensures your data stays safe and fast. We’ll cover setting up browsers, torrent clients, and gaming platforms.
Using browsers
Firefox lets you set up socks5 in its network settings. Just enter the SOCKS host and port. Also, make sure to select “Proxy DNS when using SOCKS v5” to avoid DNS leaks.
Chrome and other Chromium browsers use system proxy settings. Or, you can install FoxyProxy to direct specific tabs through the proxy.
Always test your browser with an IP-reveal site to see if it’s using the proxy. If you use extensions, keep them updated. This helps protect your data when using the proxy.
Compatibility with torrent clients
Many torrent clients support SOCKS5. qBittorrent, uTorrent/BitTorrent, Vuze, and Transmission let you choose SOCKS5 as your proxy. Make sure to set it for peer connections, DHT, and trackers.
Remember to enable authentication if your provider needs it. Also, disable direct connections to prevent leaks. Use torrent IP-checker sites to check if your proxy is working.
Configuring for gaming platforms
Many games don’t have proxy settings. But, you can use Proxifier on Windows or proxychains on Linux to route game traffic. SSH dynamic forwarding can also create a local SOCKS5 endpoint.
UDP traffic is key for fast gaming. Choose solutions that support UDP relay or SOCKS5 UDP. Always test latency before using a provider for competitive games. Also, check stability and adjust settings as needed.
| Application Type | Typical Clients / Tools | Key Settings | Best Practice |
|---|---|---|---|
| Web Browsing | Firefox, Chrome (via system), FoxyProxy | Set SOCKS5 host/port, enable proxy DNS | Test with IP reveal and limit extension permissions |
| Torrenting | qBittorrent, uTorrent/BitTorrent, Vuze, Transmission | Proxy type = SOCKS5, enable for peers/DHT/trackers, use auth | Disable direct connections and verify with torrent IP checker |
| Gaming | Proxifier, proxychains, SSH dynamic forwarding | Route game executable through SOCKS5, enable UDP relay if supported | Run latency and stability tests before competitive use |
Potential Downsides of SOCKS5
We will outline practical drawbacks to weigh when choosing a SOCKS5 proxy for daily use. The protocol can solve many routing problems, but it brings trade-offs that matter for privacy, setup, and reliability.

Limitations in Security
A SOCKS5 proxy does not encrypt traffic by default. This means payloads and metadata can be seen by others. Using an untrusted provider can lead to sensitive data being logged or inspected.
To protect yourself, pair a SOCKS5 proxy with TLS, HTTPS, or a VPN for confidential traffic. This extra layer helps reduce the security risks of the protocol.
Configuration Complexity
Setting up proxy settings for each app can be a challenge. You need to configure each program separately and manage DNS and proxy settings carefully. Mistakes can let requests bypass the proxy.
Setting up system-wide SOCKS5 on macOS and Windows can be tricky. Sometimes, you need third-party tools like Proxifier. Non-technical users may find it hard to use and troubleshoot.
Reliability of Free Proxies
Be cautious with free proxies. They often have issues like intermittent availability, slow speeds, and frequent IP blacklisting. Providers might log your data or inject ads, which can harm your privacy and experience.
For activities like torrenting or gaming, where stability and speed are crucial, free proxies are not reliable. Paid, reputable services are better for these needs to avoid the common problems of free proxies.
Understanding Legal Implications
It’s important to know the legal limits when talking about SOCKS5 proxy use. Using a SOCKS5 proxy for privacy or speed is legal in most places, like the United States. But, the activity itself must follow the law.
It’s crucial to stay away from illegal activities, even with a proxy. Actions like sharing copyrighted content without permission, hacking, or trying to avoid law enforcement are still illegal. These actions can get individuals and companies in trouble, even if they use proxies to hide their actions.
Before using proxies, we should think about the laws in different places. Some countries, like China, Iran, and Russia, have strict rules about using proxies and VPNs. They might punish people for trying to get around local rules.
If you work or travel abroad, it’s smart to check the local laws. Businesses need to think about these laws when choosing proxy services. This affects their policies and who they work with.
Creating clear rules for using proxies is a good idea. Make sure everyone knows what’s allowed and why proxies are used. Companies should have rules for logging, keeping data, and handling legal requests.
For more complex cases, getting legal advice is a good idea. Lawyers can help make sure proxy use follows laws like GDPR when dealing with personal data. This helps avoid legal problems and keeps companies in line with rules everywhere.
Best SOCKS5 Proxy Services
We compare top SOCKS5 proxy services for users. We look at performance, support, and pricing. This helps readers choose the right provider for their needs.
NordVPN/NordLayer, Private Internet Access (PIA), Proxy.sh, and TorGuard are compared. Each offers SOCKS5 proxy access or similar services. We consider server network size, UDP support, and setup guides.
NordVPN and NordLayer have large server networks and detailed guides. PIA offers SOCKS5 with strong privacy and easy setup. Proxy.sh focuses on flexible proxy plans with clear billing. TorGuard is great for torrenting and power users needing fast connections.
Good setup guides are key. They help both beginners and experts. Providers with clear tutorials save time and reduce support calls.
Customer support should be easy to reach. Live chat, email, and tickets help solve problems fast. Knowledge bases and videos show a provider’s commitment to support.
Reliability is crucial. Providers with strong uptime records ensure smooth use. Good customer support adds to the reliability for all-day needs.
Pricing plans are compared by looking at monthly vs. annual rates. We also check bandwidth, connections, and extra features. Many offer discounts for annual plans, while monthly plans are flexible for short projects.
It’s wise to check refund policies and free trials. A short trial lets us test a proxy’s performance. Users who torrent should look for plans with plenty of bandwidth and clear terms.
Here’s a table comparing key features of each provider. It helps us quickly see the differences.
| Provider | SOCKS5 Access | Key Strengths | Support Channels | Typical Pricing Structure |
|---|---|---|---|---|
| NordVPN / NordLayer | Included | Extensive server network, strong docs, fast backbone | Live chat, email, knowledge base | Monthly & annual subscriptions, business tiers |
| Private Internet Access (PIA) | Included | Privacy-focused, simple setup, good value | Live chat, ticketing, guides | Monthly & annual, family plans, add-ons |
| Proxy.sh | Available | Flexible proxy options, pay-as-you-go choices | Email, docs, ticketing | Tiered plans, bandwidth-based options |
| TorGuard | Specialized SOCKS5 | Torrent-focused, customizable locations | Live chat, email, extensive guides | Monthly & annual, add-ons like dedicated IPs |
Choose a plan that matches your needs, not just the cheapest. Look at bandwidth, connections, and refunds. A trial period can confirm if a service meets your speed needs.
FAQs About SOCKS5 Proxies
We answer the most frequent queries to help readers get practical clarity. This FAQ section covers usage, limitations, and setup tips. It aims to resolve common questions with usable steps and references.
Common Questions and Misconceptions
Does SOCKS5 encrypt traffic? The socks5 protocol does not provide encryption by default. It routes traffic at the application level and can pass TCP and UDP streams without altering payloads.
Is SOCKS5 good for torrenting? Yes, SOCKS5 is popular for torrenting because it hides the client IP. We must configure the torrent client to use authentication and check that peer exchange or tracker settings do not leak the real IP.
Can SOCKS5 prevent DDoS? Using a proxy can reduce direct exposure by masking an endpoint IP. It is not a full DDoS mitigation solution. We recommend combining proxies with dedicated DDoS protection for critical services.
How is SOCKS5 different from a VPN? SOCKS5 is lighter-weight and operates per application. A VPN creates a system-wide encrypted tunnel. For sensitive data, pairing SOCKS5 with TLS or a VPN gives stronger protection.
Expert Answers to User Queries
Always enable authentication when your provider supports it. Authentication limits unauthorized use and reduces the chance of service abuse.
Combine SOCKS5 with encryption for private transactions. We suggest TLS, SSH tunnels, or a reputable VPN when handling logins, banking, or sensitive transfers.
Test DNS routing to prevent leaks. Use tools like curl or traceroute to confirm requests resolve through the intended proxy path. Misrouted DNS queries reveal real locations.
Select reputed providers for transactional privacy. Brands such as NordVPN, Private Internet Access, and TorGuard maintain support resources and clear policies we can review before subscribing.
Configuration examples are available for common clients. Firefox, qBittorrent, and Proxifier offer native or extension-based SOCKS5 support. We advise following provider guides and running quick connectivity checks after setup.
Finding Additional Resources
We recommend consulting official documentation for SOCKS implementations and the original RFCs for technical depth on the socks5 protocol. Provider support pages from NordVPN, Private Internet Access, and TorGuard offer setup articles and best practices.
Use networking tools to validate setups. Wireshark helps inspect packet flows, traceroute reveals path hops, and curl verifies HTTP requests through a proxy. These diagnostics help us identify leaks and misconfigurations.
For hands-on troubleshooting, consult client manuals for Firefox, qBittorrent, and Proxifier. Support centers at major providers contain step-by-step walkthroughs and FAQ sections that complement this SOCKS5 proxy FAQ.
Future Trends in Proxy Services
Proxy services are set to change fast as people want more privacy and flexible networks. Online tracking is getting worse, and new rules on data protection are coming. Remote work and a growing interest in privacy tools are also driving changes.
Growing Demand for Online Privacy
More people are looking for ways to limit tracking and keep their data safe. Companies, small businesses, and individuals are using proxies and VPNs to meet their needs.
Groups like the FTC and the European GDPR are making companies more open about how they handle data. This means more focus on logging and provider policies.
Innovations in Proxy Technologies
We’re expecting big tech improvements to make proxies more reliable and secure. Secure transport layers and automated geo-located routing will make connections faster and more stable.
Developers will want API-driven proxy orchestration from providers like Bright Data and Oxylabs for big automation projects. Better UDP relay performance will help real-time apps. Hybrid solutions combining socks5 protocol with TLS tunnels or lightweight VPN encryption will become popular.
Predictions for SOCKS5 Proxies
The socks5 protocol will stay important because it’s flexible. Users who care about security will choose SOCKS5 proxies with encryption by default.
Big companies will pick more advanced options that include SOCKS5 proxy features and identity management from Microsoft and Okta. We also expect providers to be more transparent about their logs and offer clearer compliance options for businesses.
| Trend | What It Means | Expected Timeline |
|---|---|---|
| Privacy-Driven Adoption | Higher consumer and enterprise uptake of proxies and VPNs to counter tracking | 1–3 years |
| Encrypted Default Deployments | SOCKS5 proxy services bundled with TLS or similar encryption by default | 1–2 years |
| API-Oriented Management | Providers offering orchestration APIs for developers and DevOps | Immediate to 2 years |
| Hybrid Networking Solutions | Mix of socks5 protocol routing and lightweight VPN-like tunnels for latency-sensitive apps | 2–4 years |
| Regulatory Scrutiny | Stricter oversight of logging and data retention policies for proxy providers | 1–3 years |
User Experiences with SOCKS5 Proxies
We collected stories and feedback from teams and individuals. They shared how a SOCKS5 proxy works in everyday life. These stories highlight real setups, common challenges, and the benefits of using a SOCKS5 proxy over basic proxies or some VPNs.
Case Studies and Testimonials
A remote development team used a SOCKS5 proxy for secure access to internal tools. This setup kept their work smooth and protected their internal IPs. It also allowed them to route specific services securely.
A gamer found a gaming proxy to reduce DDoS attacks during matches. Using a SOCKS5 endpoint for multiplayer sessions hid their real IP. This made matchmaking more stable in certain areas.
A power user set up qBittorrent with a SOCKS5 proxy for P2P transfers. This acted as a torrenting proxy, controlling peer visibility. It also used client-level authentication for better control.
Another group used NordVPN’s SOCKS5 endpoint for selective app routing. They liked that it routed only certain traffic. This kept other connections fast and low-latency.
Common Feedback from Users
Users say SOCKS5 proxies offer better anonymity and control. They like choosing which apps use the proxy.
However, setting up a SOCKS5 proxy can be tricky. Many ask for clearer guides for client setup and DNS handling.
Streaming service tests show mixed results. Some platforms work with SOCKS5, but others block access.
When set up right, SOCKS5 proxies can be faster than some VPNs. This is because they have less overhead and selective routing without full encryption.
Users often ask for better DNS leak protection and more detailed provider guides. These help with easier setup.
Lessons Learned from Real Users
Always test for IP and DNS leaks after setting up a SOCKS5 proxy. This ensures you don’t accidentally expose your IP when using a torrenting proxy or P2P tools.
Most users suggest choosing paid providers for reliability. Paid services usually offer stable endpoints, clear documentation, and good support.
Enable authentication when possible and use encryption with SSH tunnels. This increases safety without losing performance.
Remember to follow legal and provider policies when using a SOCKS5 proxy. Knowing local laws and service terms helps avoid problems.
| Use Case | Real Setup | Main Benefit | Common Caveat |
|---|---|---|---|
| Remote development | SSH dynamic forwarding to SOCKS5 endpoint | Selective routing to internal tools | Requires SSH knowledge and proper key management |
| Gaming | Routing game client via gaming proxy | Reduced DDoS exposure and stable routing | Possible added latency if endpoint is distant |
| Torrenting | qBittorrent bound to SOCKS5 as torrenting proxy | Lower direct IP exposure to peers | Must test for DNS/IP leaks and respect laws |
| Selective app routing | NordVPN SOCKS5 endpoint for specific apps | Faster proxy paths for chosen services | Streaming results vary by platform |
Conclusion and Final Thoughts
We’ve explored how the socks5 protocol works and its benefits. A SOCKS5 proxy is great for certain needs. It supports both TCP and UDP, improving app performance. However, it’s not encrypted like a secure socket layer.
Choosing trusted paid providers is key. Make sure to set up DNS and authentication right. This keeps your data safe and your identity hidden.
When using SOCKS5 proxies, always pair them with encryption for sensitive data. For tasks like torrenting or gaming, pick reliable providers like NordVPN or TorGuard. Always enable authentication, test, and update your software.
Remember to follow the law and document your setup. This reduces risks. For more knowledge, check out provider guides and tools like Wireshark.
Reviewing RFCs or protocol details can also help. Test in safe environments and seek legal advice for big projects. This ensures you’re using SOCKS5 proxies safely and legally.
FAQ
What is a SOCKS5 proxy and how does the SOCKS5 protocol work?
A SOCKS5 proxy is a way to hide your IP address by routing your internet traffic through a server. It works by setting up a connection, doing any needed authentication, and then sending your traffic to its destination. SOCKS5 is great for hiding your IP but doesn’t encrypt your data on its own. You might need to use something like a VPN to keep your data safe.
How is SOCKS5 different from SOCKS4 and HTTP proxies?
SOCKS5 is better than SOCKS4 because it supports UDP and has more ways to authenticate. It also works with IPv6 and can handle more types of traffic. Unlike HTTP proxies, SOCKS5 can handle non-web traffic, making it more versatile.
Does SOCKS5 encrypt my traffic?
No, SOCKS5 doesn’t encrypt your data. It just routes it. To keep your data safe, you need to use encryption or a VPN. Each option has its own trade-offs.
Is SOCKS5 a good option for torrenting?
Yes, SOCKS5 is good for torrenting because it supports UDP and can be set up for specific apps. It’s often faster than VPNs and can hide your IP. But, remember to use encryption and authentication to keep your data safe.
Can SOCKS5 help with gaming latency or DDoS protection?
SOCKS5 can help with DDoS attacks by hiding your IP. It can also make your game traffic faster by routing it through closer servers. But, the results can vary, so test it out before relying on it for big games.
Should we choose a free or paid SOCKS5 proxy?
For better performance and privacy, go with a paid proxy. Free ones often have bandwidth limits, are unreliable, and might even inject malware. Paid services usually offer better service and privacy.
What features should we look for when choosing a SOCKS5 provider?
Look for support for TCP and UDP, strong authentication, clear privacy policies, and a wide range of servers. Also, check for DNS leak protection and easy setup guides. Good customer support and transparency are key.
How do we set up SOCKS5 for a specific application like a browser or torrent client?
First, get your server details from your provider. Then, set up your app to use the proxy. Firefox and some torrent clients make this easy. For apps that don’t support SOCKS5, use tools like Proxifier or proxychains.
How do we prevent DNS leaks when using SOCKS5?
To avoid DNS leaks, make sure your app proxies DNS requests. You can also use DNS over HTTPS or choose a provider that routes DNS through the proxy. Always test your setup to ensure your DNS is being proxied.
What are common configuration mistakes and troubleshooting steps?
Common mistakes include wrong server details or forgetting to enable the proxy. To fix, check your credentials and server details. If problems persist, try another app or use tools like curl or Wireshark for deeper checks. Contact your provider for help.
Is using a SOCKS5 proxy legal?
Using a SOCKS5 proxy is legal in most places, including the US, for lawful activities. But, it’s illegal for illegal activities like copyright infringement. Always check the laws in your area.
Can SOCKS5 prevent DDoS attacks?
SOCKS5 can help hide your IP from DDoS attacks. But, it’s not a full DDoS protection service. For strong protection, use a DDoS mitigation service or your provider’s safeguards.
How does SOCKS5 compare to a VPN in performance and privacy?
SOCKS5 is faster and has less overhead than a VPN. But, VPNs encrypt all your traffic and offer stronger privacy. You might want to use both for the best performance and privacy.
Which providers offer reliable SOCKS5 services?
Good providers include NordVPN, Private Internet Access, Windscribe, and TorGuard. Look for a big server network, UDP support, clear policies, and good customer support.
What performance tests should we run to evaluate a SOCKS5 proxy?
Test the proxy’s speed, ping, and packet loss. Also, do traceroutes and file transfer tests. Try different servers to find the fastest one for your needs.
Can enterprises use SOCKS5 securely at scale?
Yes, with the right setup and encryption, enterprises can use SOCKS5 securely. Make sure to have strong authentication, logging policies, and access controls. Independent audits and clear contracts are important for trust.
What are the future trends for SOCKS5 and proxy services?
Online privacy will keep growing, leading to new proxy technologies. Expect better encryption, UDP support, and easier geo-routing. SOCKS5 will likely stay useful but will be paired with stronger privacy measures.